Alert Logic Managed Web Application Firewall (WAF) for Microsoft Azure High Availability

Create two Managed WAF virtual appliances
To create the virtual appliances:
- Log in to the Microsoft Azure marketplace portal.
- At the bottom of the screen, click + New.
- Click Everything.
- In Search Everything, type Alert Logic.
- Select Alert Logic Web Security Manager - BYOL.
- Click Create.
- Complete the missing fields:
- Host Name
- User Name
- Password
- Select a Pricing Tier. By default, Standard A2 is selected

For more information regarding size information, see Virtual appliance requirements.
- In Optional Configuration, click your storage account, click Network, click Virtual Network, and then select your desired network. This step will automatically configure your Resource Group, Subscription, and Location.
- Click Create.
- Click Purchase.
- Repeat these instructions in order to create a second virtual appliance. Be sure to use a different host name, user name, and password for the second virtual appliance.
Contact Alert Logic to claim your appliance
You must contact Alert Logic in order to claim your virtual appliances. Before you contact Alert Logic, you must have available the virtual IP addresses and DNS names of the virtual appliances.
To gather the required information:
- Log in to the Microsoft Azure marketplace portal.
- In the left navigation, select Browse.
- Click Virtual machines.
- Select your virtual machine, and then copy the Virtual IP address and DNS name for later use.
- Repeat step 4 for your second virtual machine.
To contact Alert Logic to claim your appliance:
- In the US, call (877) 484-8383 and select the appropriate option.
- In the EU, call +44 (0) 203 011 5533 and do the same.
Alert Logic provisioning completes your Managed WAF virtual appliances installation and performs initial connectivity testing.
Connect Traffic Manager
In order for the Microsoft Azure Traffic Manager to load balance traffic effectively, you need to add a test page (probe / poll page) for your two virtual appliances. This step will ensure that the Traffic Manager knows that the virtual appliances are fully reachable.

For more information, see Microsoft's documentation.
To connect Traffic Manager:
- Log in to the Windows Azure management portal screen.
- Click + New.
- Click Network Services.
- Click Traffic Manager.
- Click Quick Create.
- In DNS Prefix, enter a descriptive name.
- In Load Balancing Method, select Failover.
- Click Create.
- In the table, click the Traffic Manager you just created.
- Click Configure.
- Scroll to monitoring settings.
- In Relative Path and File Name, type a file in your web server for test purposes. For example, if the file probe.html exists in your web server, type probe.html, and hit Enter on your keyboard.
- Click Save.
Create Traffic Manager endpoints
Traffic Manager endpoints communicate with the Managed WAF virtual appliances in order to load balance traffic.
- In the Windows Azure management portal, at the top, click Endpoints.
- Click Add Endpoints.
- In Service Type, select Cloud Service.
- Under Service Endpoints, select the virtual appliances you previously created.
- Click the check mark icon to save your settings.
- Under Status, verify that each endpoint is Online.
Add a website
There are four major steps to complete:
- Access the Add Website page
- Modify the vritual web server section
- Modify the real web servers section
- Modify the Initial configuration section
Step 1: Access the Add Website page
To access the Add Website page:
- At the top of the Alert Logic console, from the drop-down menu, select WAF.
- In the left navigation, under Manage, click Appliances.
- Click Manage Appliance that corresponds to the desired virtual appliance.
- In the left navigation, under Services, click Websites.
- Click Add Website.
Step 2: Modify the virtual web server section
In this step, add the website you want to protect. Managed WAF is deployed in reverse proxy mode. In reverse proxy mode, Managed WAF terminates requests and proxies the requests to the backend web server.
To modify the virtual web server section:
- In Add Website, from the Web Server Protocol list, select one of the following:
- HTTP: This option creates a website proxy that responds to HTTP requests.
- HTTPS: This option creates a website proxy that responds to HTTPS requests. Selection generates a temporary SSL certificate.
- Both: This option creates a website proxy that responds to HTTP and HTTPS requests. Selection generates a temporary SSL certificate.
- In Web server domain name, type the URL of the website you want to protect.

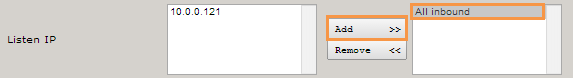
- In the Listen IP left column, do one of the following:
- Select an IP, and then click Add to add this IP to the Active Listen IP list in the right column. You can add more than one IP to the right column.
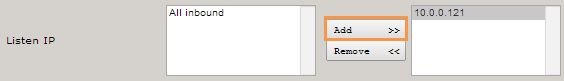
- If the left column includes multiple IP addresses, you can select All Inbound, and then click Add to add all IP addresses to the Active Listen IP list in the right column. This option allows the virtual web server to listen to all IP addresses configured to accept inbound requests.
- In HTTP(S) listen port, type the port. The default ports are as follows:
- HTTP: 80
- HTTPS: 443

Selection of Both from the Web Server Protocol list makes both the HTTP and HTTPS boxes available.
- Select Default Host for listen IP.

When enabled the virtual host responds to all requests for the virtual host not configured as the primary host name or as a virtual host for other proxies listening to the same IP address. The Test your website proxystep assumes this option is selected. This behavior is convenient for testing since it will send any request that is not a policy violation to the backend web server.
Step 3: Modify the real web servers section
Use the real web servers section to identify any backend web server to be protected by Web Security Manager.
To modify the real web servers section:
- From the Real web server protocol list, select the connection protocol you want Web Security Manager to use for to a backend web server.
- If you want traffic to a backend web server(s) to be encrypted, select https or both.
- If traffic does not require encryption, select http.
- Select Validate real servers if you want Web Security Manager to send an HTTP request to the backend web server to verify it responds to HTTP requests.

Clear the check box if the backend web server is not yet running.
- In Real server IP or public domain name, type the private IP address or DNS name on which the web server is listening.
- In Port, type the port on which the web server is listening . The default ports are as follows:
- HTTP: 80
- HTTPS: 443
- From the Role list, select one of the following:
- Active: Web Security Manager forwards requests to the backend web server.
- Backup: Web Security Manager forwards requests to the backend web server only if no other servers are active.
- Down: Web Security Manager does not forward requests to the backend web server.
Step 4: Modify the Initial configuration section
To modify the initial configuration section:
- Under Initial configuration, make sure WAF Default is selected.

You can return to this option if you need to make changes.
- Click Save Configuration, and then click Apply changes.

You can return to this option if you need to make changes.
- Click Save Configuration, and then click Apply changes.
Test your website proxy
You must test to verify Managed WAF can connect to the backend web server.

The following walkthrough assumes you have configured your website to be used as the default virtual host for the listen IP. You should also make sure that your website proxy is in Detect mode.
There are four major steps to complete:
- Edit the local hosts file
- Test for initial connectivity
- Test in Detect mode
- Test in Protect mode
Step 1: Edit the local hosts file
Edit the local hosts file to test traffic routed from the host provider through Managed WAF. This achieves the same result as reconfiguring NAT rules or making a host provider DNS change, but only the local PC is affected. This allows you to test Managed WAF prior to making a permanent NAT or DNS change.
To edit your local hosts file:
- Locate your hosts file. The host file can typically be found in the following locations:
- For Windows PC users: %SystemRoot%\system32\drivers\etc\hosts
- For Unix/Linux/Mac OS users: /etc/hosts
- Copy and save your original hosts file to another location.
- Edit the hosts file and route the host provider (www.example.com) through the Managed WAFweb application firewall (WAF) listen IP address (192.0.43.11).
- Save the hosts file.
- Once you complete testing, replace the edited hosts with the original hosts file.
Step 2: Test for initial connectivity
To test for initial connectivity:
- In your web browser's address bar, type your public web server IP, and then press Enter. The browser should open the default website for your Real web server. This test will not affect production traffic.
Step 3: Test in Detect mode
To test in Detect mode:
- In your browser's address bar, type your public web server IP followed by /?x=a%00, and then press Enter.

www.example.com/?x=a%00
The browser should open the default website for your Real web server and the simulated DOS attack should be registered on the Deny log as a DOS attempt.
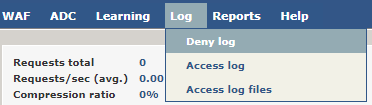
- On the Websites page, in the main menu, point to Log, and click Deny Log. To view details of any Deny log entry, click the Details icon (
 ).
). 
Step 4: Test in Protect mode
To test Protect mode:
- Open the Websites page.
- In the Websites list, for the website you want to test, in the Mode list, select Protect.
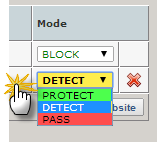
-
In your browser's address bar, type your public web server IP, followed by /?x=a%00, and then press Enter.

www.example.com/?x=a%00
The browser should show a 404 error message. This attack should also be registered on the Deny log as a DOS attempt.